Did extreme overclockers inspire Microsoft to develop closed loop liquid cooling for data centers? I'd like to think so - Related to can, overclockers, a, new, stop
Anthropic has a new security system it says can stop almost all AI jailbreaks

Anthropic unveils new proof-of-concept security measure tested on Claude Sonnet.
“Constitutional classifiers” are an attempt to teach LLMs value systems.
Tests resulted in more than an 80% reduction in successful jailbreaks.
In a bid to tackle abusive natural language prompts in AI tools, OpenAI rival Anthropic has unveiled a new concept it calls “constitutional classifiers”; a means of instilling a set of human-like values (literally, a constitution) into a large language model.
Anthropic’s Safeguards Research Team unveiled the new security measure, designed to curb jailbreaks (or achieving output that goes outside of an LLM’s established safeguards) of Claude Sonnet, its latest and greatest large language model, in a new academic paper.
The authors found an reduction in successful jailbreaks against its Claude model after implementing constitutional classifiers, while also finding the system has a minimal performance impact. With only “an absolute increase in production-traffic refusals and a inference overhead.”.
While LLMs can produce a staggering variety of abusive content, Anthropic (and contemporaries like OpenAI) are increasingly occupied by risks associated with chemical, biological, radiological and nuclear (CBRN) content. An example would be a LLM telling you how to make a chemical agent.
So, in a bid to prove the worth of constitutional classifiers. Anthropic has released a demo challenging consumers to beat 8 levels worth of CBRN-content related jailbreaking. It’s a move that has attracted criticism from those who see it as crowdsourcing its security volunteers, or ‘red teamers’.
“So you’re having the community do your work for you with no reward, so you can make more profits on closed source models?”. Wrote one Twitter user.
Anthropic noted successful jailbreaks against its constitutional classifiers defense worked around those classifiers rather than explicitly circumventing them, citing two jailbreak methods in particular. There’s benign paraphrasing (the authors gave the example of changing references to the extraction of ricin, a toxin, from castor bean mash, to protein) as well as length exploitation, which amounts to confusing the LLM model with extraneous detail.
Anthropic did add jailbreaks known to work on models without constitutional classifiers (such as many-shot jailbreaking, which entails a language prompt being a supposed dialogue between the model and the user, or ‘God-mode’, in which jailbreakers use ‘l33tspeak’ to bypass a model’s guardrails) were not successful here.
However, it also admitted that prompts submitted during the constitutional classifier tests had “impractically high refusal rates”, and. Recognised the potential for false positives and negatives in its rubric-based testing system.
In case you missed it, another LLM model, DeepSeek R1, has arrived on the scene from China, making waves thanks to being open source and capable of running on modest hardware. The centralized web and app versions of DeepSeek have faced their own fair share of jailbreaks, including using the ‘God-mode’ technique to get around their safeguards against discussing controversial aspects of Chinese history and politics.
The Razer Orochi V2 is going to be a really exciting mouse. Especially for people who wants somethin...
The CXL consortium has had a regular presence at FMS (which rechristened itself from 'Flash Memory S...
Intel has divested its entire stake in Arm Holdings during the second quarter, raising approximately...
Did extreme overclockers inspire Microsoft to develop closed loop liquid cooling for data centers? I'd like to think so
Zero-water evaporation system will virtually eliminate water usage across Microsoft-owned data centers.
This will save tens of billions of liters of water over the lifetime of Microsoft's parc of data centers.
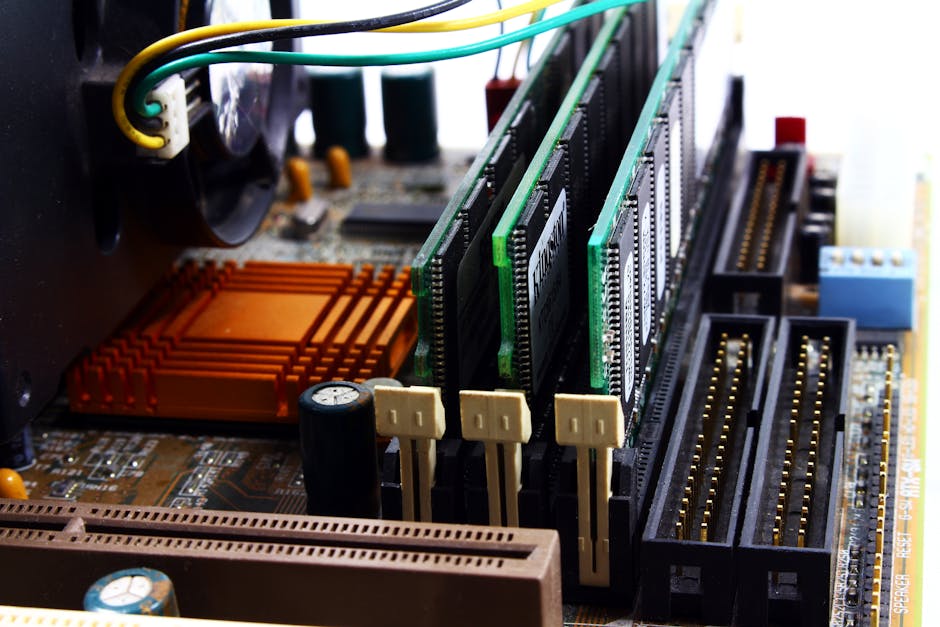
The key to delivering this solution was implementing chip level cooling solutions at scale.
Microsoft has introduced a new data center design which eliminates the need for water evaporation in cooling, addressing concerns about water usage in regions facing shortages and droughts.
This new cooling system, launched in August 2024, optimizes AI workloads while conserving water. And forms part of Microsoft's Datacenter Community Pledge, helping to support local communities and reducing environmental impact.
The system works by using chip-level liquid cooling, which provides precise temperature control without relying on water evaporation. While water is still used for administrative needs such as restrooms and kitchens, the cooling system itself does not require fresh water.
The system operates on a closed loop, meaning water is circulated continuously between servers and. Chillers without needing to be replenished. Closed-loop liquid cooling has been used by overclockers (including me) for years to keep temperatures stable during resource-heavy workloads, making it a natural fit for modern data centers with their intensive AI demands.
Water efficiency in data centers is measured using Water Usage Effectiveness (WUE). Which calculates water consumption relative to energy use. Microsoft says by moving to closed loop liquid cooling it expects to save over 125 million liters of water per year, per data center.
"We have been working since the early 2000s to reduce water use and improved our WUE by 80% since our first generation of data centers,” stated Steve Solomon, Vice President. Datacenter Infrastructure Engineering, Microsoft.
“As water challenges grow more extreme, we know we have more work to do. The shift to the next generation data centers is expected to help reduce our WUE to near zero for each data center employing zero-water evaporation. As our fleet expands over time, this shift will help reduce Microsoft’s fleetwide WUE even further."
New data centers in Phoenix, Arizona, and Mt. Pleasant, Wisconsin, will serve as pilot sites for this technology in 2026. All future Microsoft data centers will adopt this cooling approach going forward, with the first sites expected to be operational in 2027.
Eliminating evaporative cooling does increase power usage effectiveness (PUE). As mechanical cooling requires more energy. However, the use of high-efficiency economizing chillers and elevated cooling temperatures will offset some of this demand.
As the deployment of PCIe picks up steam in both datacenter and consumer markets, PCI-SIG is not...
I want to tell you about this keyboard, I’ve been using the XTRFY K40 TKL RGB for 2 years now. It ha...
We've been reporting on camera rumors for many years and trust us, in 2025 there are few true tech s...
Meta reveals what kinds of AI even it would think too risky to release
Meta makes its Frontier AI Framework available to all.
Building on these developments, the organization says it is concerned about AI-induced cybersecurity threats.
Risk assessments and modeling will categorize AI models as critical, high, or moderate.
Meta has revealed some concerns about the future of AI despite CEO Mark Zuckerberg’s well-publicized intentions to make artificial general intelligence (AGI) openly available to all.
The firm's newly-released Frontier AI Framework explores some “critical” risks that AI could pose, including its potential implications on cybersecurity and chemical and biological weapons.
By making its guidelines publicly available, Meta hopes to collaborate with other industry leaders to “anticipate and mitigate” such risks by identifying potential “catastrophic” outcomes and threat modeling to establish thresholds.
Meta wants to prevent “catastrophic” AI outcomes.
Stating, “open sourcing AI is not optional; it is essential,” Meta outlined in a blog post how sharing research helps organizations learn from each other’s assessments and encourages innovation.
Its framework works by proactively running periodic threat modeling exercises to complement its AI risk assessments – modeling will also be used if and when an AI model is identified to potentially “exceed current frontier capabilities,” where it becomes a threat.
Furthermore, these processes are informed by internal and external experts, resulting in one of three negative categories: ‘critical,’ where the development of the model must stop; ‘high,’ where the model in its current state must not be released; and ‘moderate,’ where further consideration is given to the release strategy.
Some threats include the discovery and exploitation of zero-day vulnerabilities, automated scams and frauds and the development of high-impact biological agents.
In the framework, Meta writes: “While the focus of this Framework is on our efforts to anticipate and. Mitigate risks of catastrophic outcomes, it is critical to emphasize that the reason to develop advanced AI systems in the first place is because of the tremendous potential for benefits to society from those technologies.”.
The enterprise has committed to updating its framework with the help of academics, policymakers, civil society organizations, governments, and the wider AI community as the technology continues to develop.
Remember Eluktronics – no not electronics, Eluktronics – one of the small companies that are trying ...
At FMS 2024, the technological requirements from the storage and memory subsystem took center stage...
Rumor has it there’ll be a press event for AMD RX 9070 GPUs at the end of February.
Market Impact Analysis
Market Growth Trend
| 2018 | 2019 | 2020 | 2021 | 2022 | 2023 | 2024 |
|---|---|---|---|---|---|---|
| 4.9% | 5.9% | 6.2% | 6.9% | 7.3% | 7.5% | 7.6% |
Quarterly Growth Rate
| Q1 2024 | Q2 2024 | Q3 2024 | Q4 2024 |
|---|---|---|---|
| 6.9% | 7.2% | 7.4% | 7.6% |
Market Segments and Growth Drivers
| Segment | Market Share | Growth Rate |
|---|---|---|
| Semiconductors | 35% | 9.3% |
| Consumer Electronics | 29% | 6.2% |
| Enterprise Hardware | 22% | 5.8% |
| Networking Equipment | 9% | 7.9% |
| Other Hardware | 5% | 5.3% |
Technology Maturity Curve
Different technologies within the ecosystem are at varying stages of maturity:
Competitive Landscape Analysis
| Company | Market Share |
|---|---|
| Apple | 18.7% |
| Samsung | 16.4% |
| Intel | 12.9% |
| NVIDIA | 9.8% |
| AMD | 7.3% |
Future Outlook and Predictions
The Think Anthropic Security landscape is evolving rapidly, driven by technological advancements, changing threat vectors, and shifting business requirements. Based on current trends and expert analyses, we can anticipate several significant developments across different time horizons:
Year-by-Year Technology Evolution
Based on current trajectory and expert analyses, we can project the following development timeline:
Technology Maturity Curve
Different technologies within the ecosystem are at varying stages of maturity, influencing adoption timelines and investment priorities:
Innovation Trigger
- Generative AI for specialized domains
- Blockchain for supply chain verification
Peak of Inflated Expectations
- Digital twins for business processes
- Quantum-resistant cryptography
Trough of Disillusionment
- Consumer AR/VR applications
- General-purpose blockchain
Slope of Enlightenment
- AI-driven analytics
- Edge computing
Plateau of Productivity
- Cloud infrastructure
- Mobile applications
Technology Evolution Timeline
- Technology adoption accelerating across industries
- digital transformation initiatives becoming mainstream
- Significant transformation of business processes through advanced technologies
- new digital business models emerging
- Fundamental shifts in how technology integrates with business and society
- emergence of new technology paradigms
Expert Perspectives
Leading experts in the hardware tech sector provide diverse perspectives on how the landscape will evolve over the coming years:
"Technology transformation will continue to accelerate, creating both challenges and opportunities."
— Industry Expert
"Organizations must balance innovation with practical implementation to achieve meaningful results."
— Technology Analyst
"The most successful adopters will focus on business outcomes rather than technology for its own sake."
— Research Director
Areas of Expert Consensus
- Acceleration of Innovation: The pace of technological evolution will continue to increase
- Practical Integration: Focus will shift from proof-of-concept to operational deployment
- Human-Technology Partnership: Most effective implementations will optimize human-machine collaboration
- Regulatory Influence: Regulatory frameworks will increasingly shape technology development
Short-Term Outlook (1-2 Years)
In the immediate future, organizations will focus on implementing and optimizing currently available technologies to address pressing hardware tech challenges:
- Technology adoption accelerating across industries
- digital transformation initiatives becoming mainstream
These developments will be characterized by incremental improvements to existing frameworks rather than revolutionary changes, with emphasis on practical deployment and measurable outcomes.
Mid-Term Outlook (3-5 Years)
As technologies mature and organizations adapt, more substantial transformations will emerge in how security is approached and implemented:
- Significant transformation of business processes through advanced technologies
- new digital business models emerging
This period will see significant changes in security architecture and operational models, with increasing automation and integration between previously siloed security functions. Organizations will shift from reactive to proactive security postures.
Long-Term Outlook (5+ Years)
Looking further ahead, more fundamental shifts will reshape how cybersecurity is conceptualized and implemented across digital ecosystems:
- Fundamental shifts in how technology integrates with business and society
- emergence of new technology paradigms
These long-term developments will likely require significant technical breakthroughs, new regulatory frameworks, and evolution in how organizations approach security as a fundamental business function rather than a technical discipline.
Key Risk Factors and Uncertainties
Several critical factors could significantly impact the trajectory of hardware tech evolution:
Organizations should monitor these factors closely and develop contingency strategies to mitigate potential negative impacts on technology implementation timelines.
Alternative Future Scenarios
The evolution of technology can follow different paths depending on various factors including regulatory developments, investment trends, technological breakthroughs, and market adoption. We analyze three potential scenarios:
Optimistic Scenario
Rapid adoption of advanced technologies with significant business impact
Key Drivers: Supportive regulatory environment, significant research breakthroughs, strong market incentives, and rapid user adoption.
Probability: 25-30%
Base Case Scenario
Measured implementation with incremental improvements
Key Drivers: Balanced regulatory approach, steady technological progress, and selective implementation based on clear ROI.
Probability: 50-60%
Conservative Scenario
Technical and organizational barriers limiting effective adoption
Key Drivers: Restrictive regulations, technical limitations, implementation challenges, and risk-averse organizational cultures.
Probability: 15-20%
Scenario Comparison Matrix
| Factor | Optimistic | Base Case | Conservative |
|---|---|---|---|
| Implementation Timeline | Accelerated | Steady | Delayed |
| Market Adoption | Widespread | Selective | Limited |
| Technology Evolution | Rapid | Progressive | Incremental |
| Regulatory Environment | Supportive | Balanced | Restrictive |
| Business Impact | Transformative | Significant | Modest |
Transformational Impact
Technology becoming increasingly embedded in all aspects of business operations. This evolution will necessitate significant changes in organizational structures, talent development, and strategic planning processes.
The convergence of multiple technological trends—including artificial intelligence, quantum computing, and ubiquitous connectivity—will create both unprecedented security challenges and innovative defensive capabilities.
Implementation Challenges
Technical complexity and organizational readiness remain key challenges. Organizations will need to develop comprehensive change management strategies to successfully navigate these transitions.
Regulatory uncertainty, particularly around emerging technologies like AI in security applications, will require flexible security architectures that can adapt to evolving compliance requirements.
Key Innovations to Watch
Artificial intelligence, distributed systems, and automation technologies leading innovation. Organizations should monitor these developments closely to maintain competitive advantages and effective security postures.
Strategic investments in research partnerships, technology pilots, and talent development will position forward-thinking organizations to leverage these innovations early in their development cycle.
Technical Glossary
Key technical terms and definitions to help understand the technologies discussed in this article.
Understanding the following technical concepts is essential for grasping the full implications of the security threats and defensive measures discussed in this article. These definitions provide context for both technical and non-technical readers.


