Secure coding beyond just memory safety - Related to beyond, secure, doom, tests, data
Solving the data doom loop

Ken Stott, Field CTO of API platform Hasura, tells Ryan about the data doom loop: the concept that organizations are spending lots of money on data systems without seeing improvements in data quality or efficiency.
Ken Stott, Field CTO of API platform Hasura, tells Ryan about the data doom loop: the concept that organizations are spending lots of money on data systems without seeing improvements in data quality or efficiency. Their conversation touches on the challenges of data management, the impact of microservices, the importance of feedback loops in ensuring data quality, and how a data architecture that uses a supergraph would enhance data accessibility and quality.
Hasura is a rapid API development and data access platform that automates backend operations for faster application building. Get started exploring here.
Read Ken’s article on the data doom loop.
Shoutout to Stack Overflow user liquorvicar, who earned a Lifeboat badge with an exemplary answer to Checking value in an array inside one SQL query with WHERE clause.
A little gem from Kevin Powell’s “HTML & of the Week” website, reminding us that using container queries opens up container query units for si......
, it’s the Valentine’s Day season again, and what enhanced way to express our love than with the symbol of love: a hear......
Geoff’s post about the CSS Working Group’s decision to work on inline conditionals inspired some drama in the comments section. Some developers are ex......
Secure coding beyond just memory safety
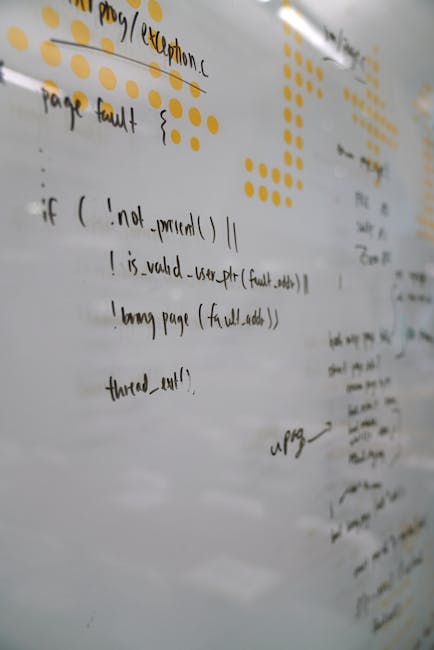
Software security expert Tanya Janca, author of Alice and Bob Learn Secure Coding and Staff DevRel at AppSec organization Semgrep, joins Ryan to talk about secure coding practices. Tanya unpacks the significance of input validation, the challenges of trusting data findings, and the intersection of security and law. Bonus: what she learned trying to secure a Canadian national election.
Semgrep is an AppSec platform that lets devs deploy static application security testing (SAST), software composition analysis (SCA), and secret scans. Explore their docs.
Tanya is the author of Alice and Bob Learn Secure Coding and Alice and Bob Learn Application Security.
She’s also written for our blog: Three layers to secure a software development organization and Continuous delivery, meet continuous security.
Secure coding might be an issue of national security.
Follow Tanya on LinkedIn or check out her website.
Stack Overflow user Reishin earned a Populist badge with their answer to piping from stdin to a python code in a bash script.
The traditional way of building Docker images using the docker build command is simple and straightforward, but when working with complex applications......
React’s custom hooks are a powerful feature that allows developers to encapsulate and reuse logic across components. By creating custom hooks, you can......
Amazon ne veut pas que les candidat(e)s aux offres d'emploi puissent utiliser l'IA / GenIA pour rédiger un CV, une lettre de motivation ou lire des ré......
Writing tests with AI, but not LLMs

Animesh Mishra, senior solutions engineer at Diffblue, joins Ryan and Ben to talk about how AI agents can help you get more effective test coverage. Animesh explains how agentic AI can expedite and enhance automation and refactoring processes, how Diffblue leverages machine learning techniques to write effective unit tests, and why clear use cases and trust are so significant in developing AI tools. Plus: Why Diffblue sees Copilot as a complement, not a competitor.
Diffblue Cover is an AI agent for testing complex Java code at scale. Check out their docs to get started automating unit tests today.
This article will help you understand the difference between Diffblue Cover and Copilot.
Stack Overflow user Keet Sugathadasa earned a Populist badge by answering a question in the CI/CD Collective: Gitlab CI CD variable are not getting injected while running gitlab pipeline.
.NET Aspire team has released version [website] of the platform. This minor revision is focused on new dashboard elements and small overall improvements acros......
The traditional way of building Docker images using the docker build command is simple and straightforward, but when working with complex applications......
Most applications rely on cloud SDKs to connect to services like message brokers, queues, databases, APIs and more. This introduces deployment frictio......
Market Impact Analysis
Market Growth Trend
| 2018 | 2019 | 2020 | 2021 | 2022 | 2023 | 2024 |
|---|---|---|---|---|---|---|
| 7.5% | 9.0% | 9.4% | 10.5% | 11.0% | 11.4% | 11.5% |
Quarterly Growth Rate
| Q1 2024 | Q2 2024 | Q3 2024 | Q4 2024 |
|---|---|---|---|
| 10.8% | 11.1% | 11.3% | 11.5% |
Market Segments and Growth Drivers
| Segment | Market Share | Growth Rate |
|---|---|---|
| Enterprise Software | 38% | 10.8% |
| Cloud Services | 31% | 17.5% |
| Developer Tools | 14% | 9.3% |
| Security Software | 12% | 13.2% |
| Other Software | 5% | 7.5% |
Technology Maturity Curve
Different technologies within the ecosystem are at varying stages of maturity:
Competitive Landscape Analysis
| Company | Market Share |
|---|---|
| Microsoft | 22.6% |
| Oracle | 14.8% |
| SAP | 12.5% |
| Salesforce | 9.7% |
| Adobe | 8.3% |
Future Outlook and Predictions
The Solving Data Doom landscape is evolving rapidly, driven by technological advancements, changing threat vectors, and shifting business requirements. Based on current trends and expert analyses, we can anticipate several significant developments across different time horizons:
Year-by-Year Technology Evolution
Based on current trajectory and expert analyses, we can project the following development timeline:
Technology Maturity Curve
Different technologies within the ecosystem are at varying stages of maturity, influencing adoption timelines and investment priorities:
Innovation Trigger
- Generative AI for specialized domains
- Blockchain for supply chain verification
Peak of Inflated Expectations
- Digital twins for business processes
- Quantum-resistant cryptography
Trough of Disillusionment
- Consumer AR/VR applications
- General-purpose blockchain
Slope of Enlightenment
- AI-driven analytics
- Edge computing
Plateau of Productivity
- Cloud infrastructure
- Mobile applications
Technology Evolution Timeline
- Technology adoption accelerating across industries
- digital transformation initiatives becoming mainstream
- Significant transformation of business processes through advanced technologies
- new digital business models emerging
- Fundamental shifts in how technology integrates with business and society
- emergence of new technology paradigms
Expert Perspectives
Leading experts in the software dev sector provide diverse perspectives on how the landscape will evolve over the coming years:
"Technology transformation will continue to accelerate, creating both challenges and opportunities."
— Industry Expert
"Organizations must balance innovation with practical implementation to achieve meaningful results."
— Technology Analyst
"The most successful adopters will focus on business outcomes rather than technology for its own sake."
— Research Director
Areas of Expert Consensus
- Acceleration of Innovation: The pace of technological evolution will continue to increase
- Practical Integration: Focus will shift from proof-of-concept to operational deployment
- Human-Technology Partnership: Most effective implementations will optimize human-machine collaboration
- Regulatory Influence: Regulatory frameworks will increasingly shape technology development
Short-Term Outlook (1-2 Years)
In the immediate future, organizations will focus on implementing and optimizing currently available technologies to address pressing software dev challenges:
- Technology adoption accelerating across industries
- digital transformation initiatives becoming mainstream
These developments will be characterized by incremental improvements to existing frameworks rather than revolutionary changes, with emphasis on practical deployment and measurable outcomes.
Mid-Term Outlook (3-5 Years)
As technologies mature and organizations adapt, more substantial transformations will emerge in how security is approached and implemented:
- Significant transformation of business processes through advanced technologies
- new digital business models emerging
This period will see significant changes in security architecture and operational models, with increasing automation and integration between previously siloed security functions. Organizations will shift from reactive to proactive security postures.
Long-Term Outlook (5+ Years)
Looking further ahead, more fundamental shifts will reshape how cybersecurity is conceptualized and implemented across digital ecosystems:
- Fundamental shifts in how technology integrates with business and society
- emergence of new technology paradigms
These long-term developments will likely require significant technical breakthroughs, new regulatory frameworks, and evolution in how organizations approach security as a fundamental business function rather than a technical discipline.
Key Risk Factors and Uncertainties
Several critical factors could significantly impact the trajectory of software dev evolution:
Organizations should monitor these factors closely and develop contingency strategies to mitigate potential negative impacts on technology implementation timelines.
Alternative Future Scenarios
The evolution of technology can follow different paths depending on various factors including regulatory developments, investment trends, technological breakthroughs, and market adoption. We analyze three potential scenarios:
Optimistic Scenario
Rapid adoption of advanced technologies with significant business impact
Key Drivers: Supportive regulatory environment, significant research breakthroughs, strong market incentives, and rapid user adoption.
Probability: 25-30%
Base Case Scenario
Measured implementation with incremental improvements
Key Drivers: Balanced regulatory approach, steady technological progress, and selective implementation based on clear ROI.
Probability: 50-60%
Conservative Scenario
Technical and organizational barriers limiting effective adoption
Key Drivers: Restrictive regulations, technical limitations, implementation challenges, and risk-averse organizational cultures.
Probability: 15-20%
Scenario Comparison Matrix
| Factor | Optimistic | Base Case | Conservative |
|---|---|---|---|
| Implementation Timeline | Accelerated | Steady | Delayed |
| Market Adoption | Widespread | Selective | Limited |
| Technology Evolution | Rapid | Progressive | Incremental |
| Regulatory Environment | Supportive | Balanced | Restrictive |
| Business Impact | Transformative | Significant | Modest |
Transformational Impact
Technology becoming increasingly embedded in all aspects of business operations. This evolution will necessitate significant changes in organizational structures, talent development, and strategic planning processes.
The convergence of multiple technological trends—including artificial intelligence, quantum computing, and ubiquitous connectivity—will create both unprecedented security challenges and innovative defensive capabilities.
Implementation Challenges
Technical complexity and organizational readiness remain key challenges. Organizations will need to develop comprehensive change management strategies to successfully navigate these transitions.
Regulatory uncertainty, particularly around emerging technologies like AI in security applications, will require flexible security architectures that can adapt to evolving compliance requirements.
Key Innovations to Watch
Artificial intelligence, distributed systems, and automation technologies leading innovation. Organizations should monitor these developments closely to maintain competitive advantages and effective security postures.
Strategic investments in research partnerships, technology pilots, and talent development will position forward-thinking organizations to leverage these innovations early in their development cycle.
Technical Glossary
Key technical terms and definitions to help understand the technologies discussed in this article.
Understanding the following technical concepts is essential for grasping the full implications of the security threats and defensive measures discussed in this article. These definitions provide context for both technical and non-technical readers.
API beginner
 How APIs enable communication between different software systems
How APIs enable communication between different software systems

